Thfor ARMere are needs to rid yourself of those annoying self cert warnings. mkcert is a zero config type tool that allows you to create legit certs for you to use internally. We will show you how to install and do a basic use scenario. We will be installing mkcert to accomplish this task. Just an FYI I am doing this on a PiMOX you can do this on a Proxmox (Intel/AMD), Some of the choices will be different.
1 – Create a VM on your Virtual Host (Do exactly what’s in the following 8 screen captures please).
Choose a name and ID for your VM
Do not use a cd at this time we will address that later
Choose UEFI very important step, Then choose EFI Storage, it is more stable if you use the same drive as the main hdd for the VM.

Choose the location of the storage for the main hdd for the VM. Also check SSD emulation this will come in handy when riding yourself of unused drive space in the VM.
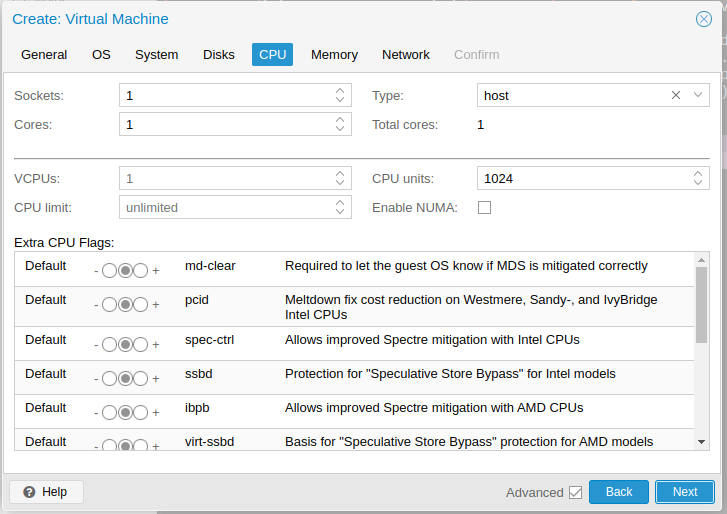
Choose your Sockets/Cores, in Type I always choose host that way OS knows what type of CPU archetecture you are using.
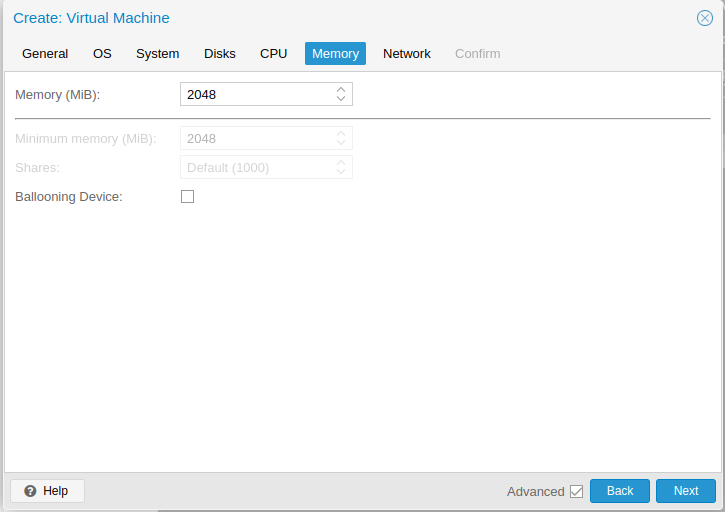
Set your memory here.
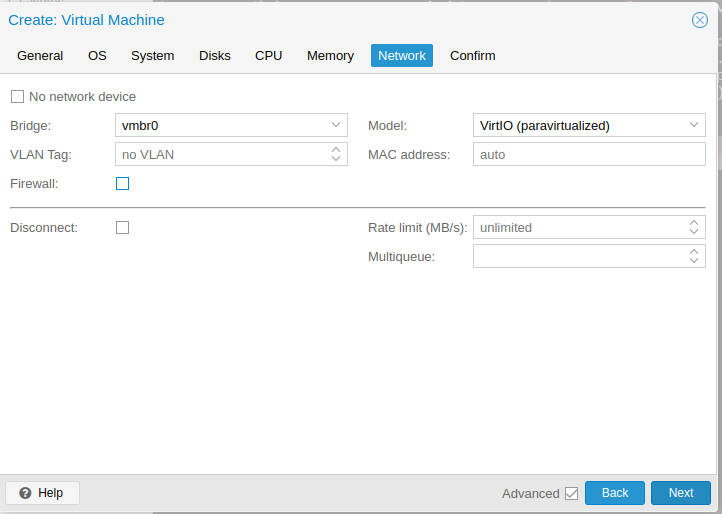
Choose the network here make sure you have the correct Network choosen.
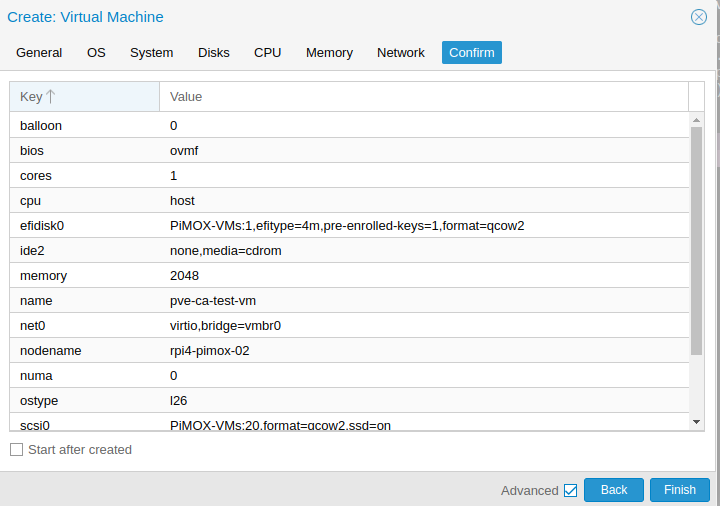
Click finish
2 – Install your preferred os (I prefer Ubuntu Server)
Install your prefered OS.
note: Update the repository and Upgrade all Packages
3 – sudo apt update -y && sudo apt full-upgrade -y
Let’s install dependencies for mkcert
4 – sudo apt install libnss3-tools -y
Let’s install mkcert – at the time of this writing the version is 1.4.4 – Make sure you get the arm version.
5 – wget https://github.com/FiloSottile/mkcert/releases/download/v1.4.4/mkcert-v1.4.4-linux-arm64
Let’s cp the executable to it’s proper location & make it executable
6 – sudo cp mkcert-v1.4.4-linux-arm64 /usr/local/bin/mkcert
7 – sudo chmod +x /usr/local/bin/mkcert
Let’s create the Local CA
8 – sudo mkcert -install
Now Let’s find the root CA
9 – sudo mkcert -CAROOT
10 – ls -al results of -CAROOT
The results should be the root-keyCA.pem and rootCA.pem
note: Let’s make your first local cert
11 – mkcert your.dom '*.your.dom' localhost 127.0.0.1 ::1
They should be in your current working directory
12 – ls -al ./your_FQDN.dom.com+*